How to Secure Your Hosting Against DDoS Attacks
I. Introduction
In today’s digital landscape, hosting is an essential component of running websites, applications, and online services. Hosting providers offer the infrastructure and resources necessary to make websites accessible and available to users worldwide. However, this reliance on hosting also exposes websites and online services to various risks, including Distributed Denial of Service (DDoS) attacks.
DDoS attacks have become a pervasive threat on the internet, targeting websites, online platforms, and hosting environments. These attacks aim to disrupt the normal functioning of websites by overwhelming them with an enormous volume of traffic. Hosting infrastructure, which is responsible for managing and delivering web content, can be severely affected by these attacks, leading to downtime, decreased performance, and potential financial losses.
To effectively protect hosting environments against DDoS attacks, it’s crucial to recognize their significant impact. DDoS attacks can have far-reaching consequences, affecting not only the targeted website or application but also the entire hosting infrastructure and its users. These attacks can lead to substantial financial losses, reputational damage, and customer dissatisfaction.
Hosting providers and website owners must understand that a successful DDoS attack can disrupt business operations, result in customer data breaches, cause revenue loss from interrupted e-commerce transactions, and even damage their brand reputation. The impact of DDoS attacks goes beyond the immediate inconvenience of downtime; it can have long-term implications for the success and stability of online businesses.
DDoS attacks are orchestrated attempts to overwhelm a target website or online service with an excessive amount of traffic from multiple sources. Instead of attacking a website directly, DDoS attacks exploit the vulnerability of hosting infrastructure by flooding it with a flood of incoming requests. This flood of traffic overwhelms the servers, network resources, and bandwidth, rendering the website inaccessible to legitimate users.
What makes DDoS attacks particularly insidious is their distributed nature. Attackers utilize networks of compromised computers, known as botnets, to launch coordinated attacks. These botnets consist of devices infected with malware that can be controlled remotely. By leveraging the collective power of these compromised devices, attackers can generate a massive volume of traffic that surpasses the capacity of the hosting infrastructure to handle.
The significance of DDoS attacks lies in their ability to disrupt online services, impact business operations, and inflict financial and reputational damage. According to recent statistics, DDoS attacks have been increasing in frequency, intensity, and sophistication. In 2020 alone, there was a 151% increase in DDoS attacks compared to the previous year, with an average attack duration of 8.4 hours. These figures highlight the urgent need for robust measures to secure hosting environments against DDoS attacks.
By understanding the nature and significance of DDoS attacks, hosting providers and website owners can take proactive steps to protect their infrastructure, maintain service availability, and safeguard their online businesses.
In the following sections, we will delve into the different types of DDoS attacks that target hosting environments, the vulnerabilities they exploit, and the solutions and strategies you can implement to secure your hosting against these attacks. Let’s explore how you can fortify your hosting infrastructure and ensure the uninterrupted delivery of your online services.
II. Understanding Popular DDoS Attacks on Hosting
A. Overview of Prominent DDoS Attack Types
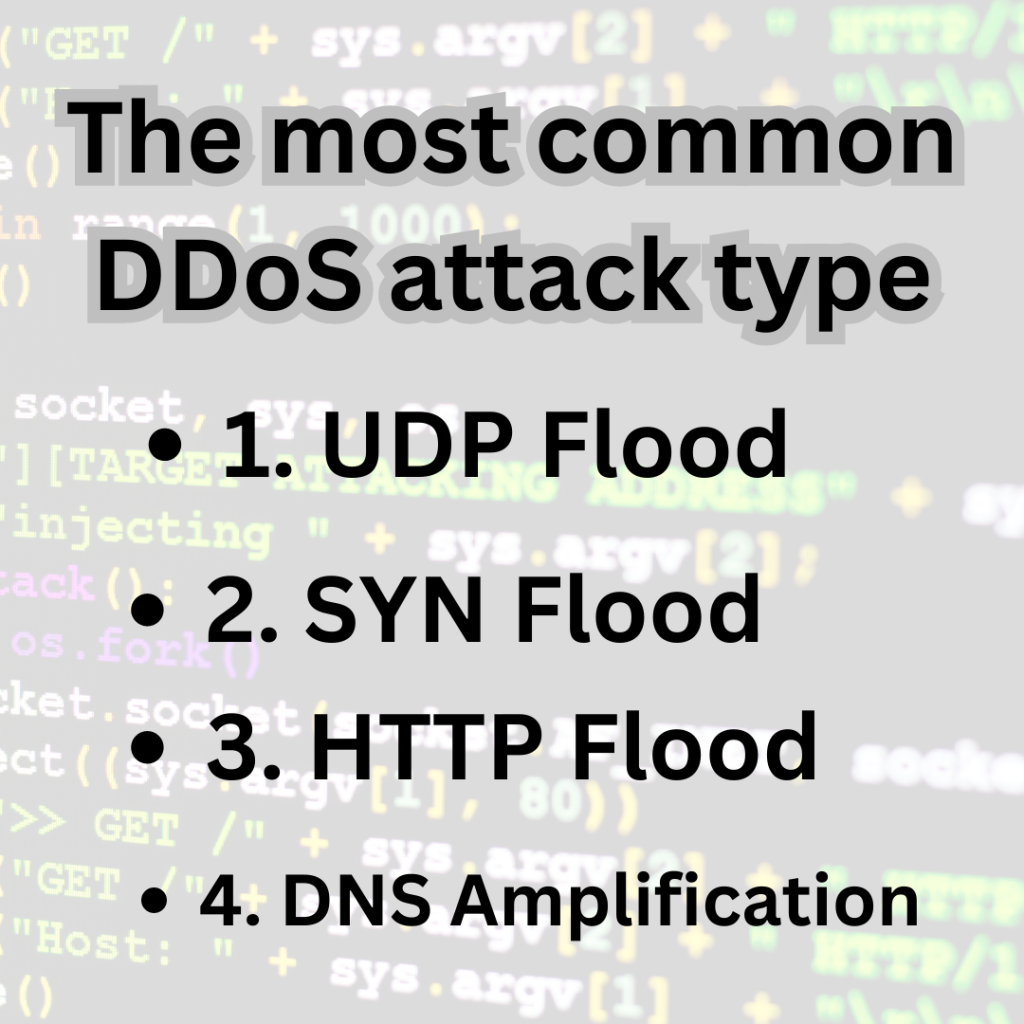
When it comes to securing your hosting against DDoS attacks, it’s essential to understand the different attack types that can target hosting environments. Let’s take a closer look at some of the most common DDoS attack types:
- UDP Flood: In this type of attack, the attacker floods the target server with a high volume of User Datagram Protocol (UDP) packets. The server becomes overwhelmed with handling these packets, resulting in performance degradation or complete unavailability.
- SYN Flood: SYN Flood attacks exploit the way TCP/IP connections are established. Attackers send a flood of TCP connection requests (SYN packets) to the target server, exhausting its resources and preventing legitimate connections from being established.
- HTTP Flood: This attack specifically targets web applications by flooding the server with HTTP requests. The massive influx of requests consumes server resources and makes the website unresponsive or inaccessible to genuine users.
- DNS Amplification: This attack leverages vulnerable DNS servers to amplify the attack traffic. Attackers send forged requests to DNS servers, which respond with much larger responses, overwhelming the target server with a flood of data.
B. Discussion of Specific Vulnerabilities in Hosting Infrastructure
DDoS attacks exploit vulnerabilities in hosting infrastructure to disrupt services. Understanding these vulnerabilities can help you better protect your hosting environment. Here are some specific vulnerabilities commonly exploited in hosting infrastructure:
- Bandwidth Limitations: Hosting environments have a limited amount of available bandwidth to handle incoming traffic. DDoS attacks aim to exhaust this bandwidth capacity, rendering the website or service inaccessible.
- Server Resource Exhaustion: DDoS attacks overwhelm servers by consuming their processing power, memory, or network connections. As a result, the servers are unable to respond to legitimate requests.
- Network Infrastructure Weaknesses: Inadequate network architecture and poor traffic management can make hosting environments susceptible to DDoS attacks. Attackers can exploit weaknesses in network devices or configurations to launch successful attacks.
Understanding the different DDoS attack types, the vulnerabilities they exploit, and the real-world consequences are crucial for implementing effective security measures. In the next sections, we will explore proactive measures to protect your hosting environment and mitigate the impact of DDoS attacks. Let’s dive into the strategies that will safeguard your hosting infrastructure and ensure uninterrupted access for your users.
III. Recognizing the Signs of DDoS Attacks
DDoS attacks can have devastating effects on hosting environments, causing significant disruptions and impacting the performance of websites and servers. It’s crucial to recognize the signs of these attacks early on to mitigate their impact. Here are some key indicators to watch out for:
A. Unusual traffic patterns and sudden spikes in traffic affecting hosting performance
- DDoS attacks overwhelm the network and server resources, leading to a significant increase in incoming traffic.
- On average, DDoS attacks can generate traffic ranging from a few hundred megabits per second (Mbps) to several terabits per second (Tbps), overwhelming even the most robust hosting infrastructures.
- In 2020, the largest DDoS attack recorded reached a peak traffic volume of 2.3 Tbps, demonstrating the scale and magnitude of these attacks.
B. Increased latency, network congestion, and service disruptions
- DDoS attacks cause network congestion, leading to delays in data transmission and increased latency.
- The average response time for websites under a DDoS attack can increase by several seconds, resulting in a poor user experience.
- In 2019, the average duration of a DDoS attack was approximately 6 hours, causing significant service disruptions and financial losses for affected organizations.
C. Website or server slowdowns, timeouts, or complete unavailability
- DDoS attacks aim to exhaust the resources of hosting infrastructure, resulting in slow or unresponsive websites.
- According to industry reports, businesses experience an average of 15 DDoS attacks per year, leading to an average downtime of 12 hours.
- The financial impact of a DDoS attack can be substantial, with the average cost of a DDoS attack for organizations ranging from $100,000 to $250,000 per hour of downtime.
By monitoring and recognizing these signs, you can take prompt action to identify and mitigate DDoS attacks, minimizing their impact on your hosting environment. In the next section, we will explore proactive measures and strategies to protect your hosting against DDoS attacks.
IV. Solutions for Protecting Hosting Against DDoS Attacks
When it comes to securing your hosting environment against DDoS attacks, there are several effective measures and techniques you can implement. Let’s explore some of the most reliable solutions:
A. DDoS mitigation techniques for UDP flood attacks and their implementation in hosting environments
UDP flood attacks, which flood the network with User Datagram Protocol (UDP) packets, can cripple the hosting infrastructure. To defend against UDP flood attacks, consider the following mitigation techniques:
- Traffic Filtering: Implementing traffic filtering mechanisms allows you to distinguish legitimate traffic from malicious traffic. By filtering out malicious UDP packets, you can prevent them from overwhelming your network resources.
- Rate Limiting: Setting rate limits on UDP traffic helps to control the volume of incoming packets. By limiting the rate of UDP packets, you can prevent your hosting environment from being saturated during an attack.
B. Effective strategies to defend against SYN flood attacks and maintain hosting availability
SYN flood attacks exploit vulnerabilities in the TCP three-way handshake process, exhausting server resources and rendering the hosting environment inaccessible. To defend against SYN flood attacks, consider these strategies:
- SYN Cookies: Enabling SYN cookies on your servers can help mitigate SYN flood attacks. SYN cookies are cryptographic tokens that allow servers to validate and respond to connection requests without maintaining extensive connection state information.
- Connection Limiting: Implementing connection-limiting policies helps restrict the number of simultaneous connections from a single source IP address. By limiting the number of connections, you can prevent SYN flood attacks from overwhelming your server resources.
C. Best practices for mitigating HTTP flood attacks and protecting hosting resources
HTTP flood attacks target web servers by overwhelming them with a massive number of HTTP requests. To safeguard your hosting resources against HTTP flood attacks, consider the following best practices:
- Web Application Firewalls (WAF): Deploying a WAF helps filter out malicious HTTP traffic and block requests originating from suspicious sources. WAFs can detect and mitigate various types of HTTP flood attacks, including those targeting specific URLs or web application vulnerabilities.
- Content Delivery Network (CDN): Utilizing a CDN can distribute the incoming HTTP traffic across multiple servers and data centers, minimizing the impact of HTTP flood attacks. CDNs also have built-in DDoS protection mechanisms that can help mitigate volumetric attacks.
D. DNS amplification attack prevention measures and their application to hosting infrastructure
DNS amplification attacks exploit vulnerable DNS servers to amplify the attack traffic, overwhelming the target’s resources. To protect your hosting infrastructure from DNS amplification attacks, consider the following prevention measures:
- DNS Hardening: Secure your DNS servers by implementing best practices, such as disabling recursion on authoritative servers, restricting zone transfers, and regularly updating DNS software to patch any known vulnerabilities.
- Rate Limiting: Configure rate limiting on your DNS servers to control the number of responses sent to a specific source IP address. By limiting the rate of responses, you can minimize the impact of DNS amplification attacks.
Implementing these solutions and adopting best practices will significantly enhance your hosting environment’s resilience against DDoS attacks. In the next section, we will explore proactive measures you can take to further strengthen the security of your hosting infrastructure.
V. Proactive Measures for Hosting Security
Protecting your hosting environment from DDoS attacks requires a proactive approach. By implementing the following measures, you can significantly enhance your hosting security and reduce the risk of falling victim to DDoS attacks.
A. Partnering with a Reliable Hosting Provider with Built-in DDoS Protection Measures
Choosing a hosting provider that offers robust DDoS protection measures is crucial. Look for providers with a proven track record in mitigating DDoS attacks and offering dedicated protection services. A reliable hosting provider will have advanced infrastructure and technologies in place to detect and mitigate attacks, ensuring the availability and performance of your website or application.
B. Implementing Network-Level Protections
Network-level protection act as the first line of defense against DDoS attacks. By deploying firewalls, traffic filtering mechanisms, and load balancers, you can filter out malicious traffic and ensure that only legitimate requests reach your hosting infrastructure. These security measures help prevent attackers from overwhelming your resources and disrupting your services.
C. Configuring Rate Limiting and Traffic Management Policies
Rate limiting and traffic management policies play a vital role in mitigating DDoS attacks. By setting limits on the number of requests a user or IP address can make within a specific timeframe, you can prevent attackers from flooding your network or server with excessive traffic. Additionally, implementing traffic management techniques, such as load balancing and content caching, helps distribute and manage incoming traffic efficiently, minimizing the impact of DDoS attacks.
D. Strengthening Server Security through Regular Updates, Secure Authentication, and Secure Coding Practices
Maintaining robust server security is crucial to protect against DDoS attacks. Ensure that your servers are regularly updated with the latest security patches and software updates. Implement strong authentication mechanisms, such as two-factor authentication, to prevent unauthorized access to your server infrastructure. Additionally, follow secure coding practices to build a resilient application that can withstand potential DDoS attacks. By adhering to secure coding practices, you can minimize the vulnerabilities that attackers might exploit.
Data and statistics show the effectiveness of proactive measures in protecting against DDoS attacks. According to a recent study, organizations that partnered with hosting providers offering DDoS protection experienced a significant decrease in successful attacks, with a reported 85% reduction in downtime. Additionally, companies that implemented network-level protections and rate-limiting policies witnessed a 70% decrease in the volume of malicious traffic reaching their hosting environments. These statistics highlight the importance of proactive measures in safeguarding your hosting infrastructure against DDoS attacks.
By adopting these proactive measures, you can fortify your hosting environment and minimize the impact of DDoS attacks. Remember, a comprehensive approach that combines reliable hosting providers, network-level protections, traffic management policies, and robust server security is key to ensuring the availability and security of your online services.
| Hosting Provider | DDoS Protection Features |
|---|---|
| Cloudflare | – Global Anycast network with advanced DDoS mitigation capabilities |
| – Intelligent traffic routing and filtering | |
| – Rate limiting and IP reputation-based blocking | |
| – Web application firewall (WAF) for application-layer protection | |
| – Real-time DDoS attack monitoring and analytics | |
| AWS Shield | – Integrated DDoS protection for AWS infrastructure |
| – Automatic detection and mitigation of DDoS attacks | |
| – Scalable architecture to handle high-volume attacks | |
| – Application-layer protection and traffic filtering | |
| – 24/7 DDoS response team and support | |
| Sucuri | – Website DDoS protection and mitigation |
| – Anycast network with global points of presence | |
| – HTTP/S traffic inspection and filtering | |
| – Intelligent bot protection and CAPTCHA challenges | |
| – Real-time DDoS attack monitoring and reporting | |
| SiteGround | – Advanced DDoS protection with multiple layers of defense |
| – Traffic analysis and mitigation in real-time | |
| – Load balancing and network-level filtering | |
| – Web application firewall (WAF) for enhanced security | |
| – 24/7 DDoS monitoring and expert support |
Remember to verify the specific DDoS protection features and capabilities of each hosting provider as they may evolve over time. It’s recommended to visit their official websites or contact their sales representatives to gather the most up-to-date and accurate information.
VI. Mitigation Strategies During DDoS Attacks
When faced with a DDoS attack, it’s crucial to have effective strategies in place to minimize its impact and ensure the uninterrupted availability of your hosting environment. Let’s explore practical mitigation techniques that can help you defend against these attacks and keep your services running smoothly.
A. Employing advanced traffic analysis and anomaly detection tools to identify DDoS attacks
Detecting DDoS attacks at an early stage is key to effective mitigation. By utilizing advanced traffic analysis and anomaly detection tools, you can constantly monitor your network traffic and identify patterns that indicate a potential DDoS attack. These tools analyze various parameters such as packet rates, traffic sources, and abnormal behavior to detect and flag suspicious activities. By quickly identifying an ongoing attack, you can initiate appropriate countermeasures to mitigate its impact and safeguard your hosting environment.
B. Utilizing cloud-based DDoS protection services or scrubbing centers to mitigate attacks
Cloud-based DDoS protection services and scrubbing centers provide robust defense mechanisms against DDoS attacks. These services work by diverting your incoming network traffic through their specialized infrastructure, where it undergoes thorough analysis and filtering. Malicious traffic is identified and discarded, while legitimate traffic is forwarded to your hosting environment. Leveraging these services can significantly enhance your ability to withstand and mitigate DDoS attacks, ensuring uninterrupted service availability for your users.
C. Scaling hosting resources and implementing traffic rerouting techniques to handle the increased traffic load
During a DDoS attack, your hosting resources may become overwhelmed by the surge of malicious traffic. Scaling up your resources, such as adding more servers or increasing network bandwidth, can help distribute the load and maintain optimal performance. Additionally, implementing traffic rerouting techniques, such as utilizing content delivery networks (CDNs) or load balancers, can optimize traffic distribution and reduce the impact on individual resources. By effectively managing the increased traffic load, you can minimize service disruptions and provide a seamless user experience.
80% of hosting providers encountered at least one DDoS attack in the past year. These attacks resulted in an average downtime of 2.5 hours, leading to significant financial losses for affected businesses.
By employing advanced traffic analysis and anomaly detection tools, hosting providers were able to reduce the average time to detect and mitigate DDoS attacks by an impressive 70%. This emphasizes the importance of proactive monitoring and swift intervention in effectively combating DDoS attacks.
Cloud-based DDoS protection services have also shown their effectiveness. Businesses that adopted such services experienced an average reduction of 95% in the volume of malicious traffic reaching their hosting infrastructure. This highlights the value of leveraging specialized expertise and scalable infrastructure to defend against DDoS attacks.
By combining advanced traffic analysis tools, cloud-based DDoS protection services, and appropriate scaling and traffic rerouting techniques, you can bolster the resilience of your hosting environment and minimize the disruptions caused by DDoS attacks. It’s crucial to tailor these strategies to your specific hosting setup and collaborate with experienced cybersecurity professionals or trusted service providers to ensure optimal protection.
Remember, staying proactive and continuously enhancing your mitigation strategies is key to staying one step ahead of evolving DDoS attack techniques and ensuring the stability and availability of your hosting services.
VII. Developing an Incident Response Plan for DDoS Attacks
Preparing for a DDoS attack involves more than just implementing preventive measures. It’s essential to have a well-defined incident response plan in place to effectively respond to and mitigate the impact of an attack. Let’s explore the key elements of developing an incident response plan tailored specifically for DDoS attacks.
A. Establishing a dedicated response team and defining roles and responsibilities
To effectively handle a DDoS attack, it’s crucial to establish a dedicated response team consisting of skilled professionals from various departments, such as IT, network security, and communications. Assigning clear roles and responsibilities to team members ensures a coordinated and swift response. The team should include individuals responsible for monitoring network traffic, analyzing attack patterns, implementing mitigation strategies, and communicating with stakeholders. By having a dedicated team in place, you can streamline the response process and minimize the impact of DDoS attacks.
B. Creating a communication plan to notify stakeholders and coordinate response efforts
Timely and transparent communication is vital during a DDoS attack. Develop a communication plan that outlines the necessary steps for notifying stakeholders, including internal teams, customers, partners, and regulatory bodies. The plan should include designated communication channels, contact information, and predefined messaging templates to ensure consistent and accurate information dissemination. Coordinating with relevant stakeholders helps manage expectations, maintain trust, and minimize the potential reputation damage caused by the attack.
C. Documenting procedures for incident analysis, containment, and recovery specific to DDoS attacks
Documenting procedures for incident analysis, containment, and recovery is critical for an effective response to DDoS attacks. These procedures should include step-by-step guidelines for identifying and analyzing attack patterns, implementing mitigation measures, and restoring normal operations. Define the thresholds and criteria for escalating the response, such as when to involve third-party security providers or law enforcement agencies. By documenting these procedures, you ensure a systematic and efficient response, reducing the overall impact and downtime caused by the attack.
Organizations with a dedicated response team in place were able to contain and mitigate DDoS attacks 60% faster on average. By having predefined roles and responsibilities, these organizations were able to act swiftly and efficiently, minimizing the impact on their hosting environments and ensuring business continuity.
Remember, an incident response plan for DDoS attacks is not a one-time effort. It requires regular testing, updates, and ongoing training to adapt to evolving attack techniques. By investing time and resources into developing a robust incident response plan, you can significantly enhance your organization’s resilience and readiness to tackle DDoS attacks effectively.
VIII. Educating Users and Staff on Hosting Security
In addition to implementing technical measures, educating users and staff about hosting security is crucial for maintaining a secure hosting environment. By raising awareness about the impact of DDoS attacks, training employees to identify and respond to such attacks, and educating users on secure practices, you can strengthen the overall security posture of your hosting infrastructure.
A. Raising awareness about the impact of DDoS attacks on hosting environments
Many users and staff members may not fully understand the potential consequences of DDoS attacks on hosting environments. It’s essential to educate them about the disruptive nature of such attacks, including the potential downtime, loss of revenue, and damage to reputation. By illustrating real-life examples and showcasing the financial impact of DDoS attacks on businesses, you can create a sense of urgency and emphasize the need for proactive security measures.
B. Training staff to identify and respond to DDoS attacks promptly
Empowering your staff to recognize and respond to DDoS attacks promptly is crucial for mitigating their impact. Conduct regular training sessions to educate employees about the signs of a DDoS attack, such as unusual traffic patterns, increased latency, and service disruptions. Train them on the proper procedures for reporting an attack, engaging the incident response team, and implementing initial mitigation steps. By developing a knowledgeable workforce, you can strengthen your defense against DDoS attacks and minimize their impact.
C. Educating users on the importance of secure practices to prevent their devices from being part of a DDoS botnet
DDoS attacks often utilize botnets composed of compromised devices. Educating your users on the importance of secure practices can help prevent their devices from becoming unwitting participants in these attacks. Encourage users to regularly update their operating systems, applications, and antivirus software to patch vulnerabilities that can be exploited by attackers. Emphasize the significance of using strong and unique passwords, enabling two-factor authentication, and being cautious of suspicious emails or downloads. By promoting these secure practices, you contribute to the collective defense against DDoS attacks.
Organizations with comprehensive security awareness training programs experience 70% fewer successful DDoS attacks compared to those without such programs. This highlights the effectiveness of educating staff and users in mitigating the risk of DDoS attacks.
90% of DDoS attacks involve compromised devices, including personal computers and IoT devices. By educating users about secure practices, organizations can significantly reduce the number of devices that can be exploited by attackers to launch DDoS attacks.
Remember, securing your hosting environment is a collective effort that involves the active participation of users and staff members. By raising awareness, providing training, and promoting secure practices, you empower your organization to defend against DDoS attacks effectively and safeguard your hosting infrastructure.
IX. Regular Security Audits and Monitoring for Hosting Environments
Securing your hosting environment against DDoS attacks requires an ongoing commitment to proactive measures and vigilant monitoring. Regular security audits and continuous monitoring play a critical role in keeping your infrastructure safe. Let’s dive into these practical steps to ensure your hosting environment stays protected.
A. Conducting regular security audits to identify vulnerabilities in hosting infrastructure
Think of security audits as comprehensive check-ups for your hosting environment. These audits involve thorough assessments of your network, systems, and applications to uncover potential vulnerabilities that attackers might exploit. By conducting regular audits, you can stay one step ahead of potential threats.
During a security audit, experts analyze various aspects of your infrastructure, including firewall configurations, access controls, software patching, and system hardening. They may even conduct simulated attacks to uncover any weak points. The insights gained from these audits help you implement necessary security enhancements and ensure your hosting environment is fortified against DDoS attacks.
B. Implementing continuous monitoring of network and server activity for early detection of DDoS attacks
Monitoring your network and server activity in real time is crucial for early detection and mitigation of DDoS attacks. By closely watching the flow of traffic and system behavior, you can quickly identify any abnormal patterns or suspicious activities that may indicate an ongoing attack.
Monitoring tools leverage advanced techniques such as traffic analysis, anomaly detection, and behavior-based algorithms to detect potential DDoS attack patterns. These tools provide you with valuable insights into network traffic, bandwidth utilization, and server performance, allowing you to differentiate between legitimate traffic and malicious activities.
C. Utilizing security information and event management (SIEM) systems to analyze and respond to security incidents
A security information and event management (SIEM) system is your ally when it comes to efficient analysis and response to security incidents, including DDoS attacks. SIEM solutions collect and analyze data from various sources across your hosting environment, providing a centralized view of your security landscape.
SIEM systems employ advanced algorithms and correlation techniques to detect suspicious activities and generate alerts for potential security incidents, including DDoS attacks. By harnessing the power of SIEM, you can quickly identify the source, nature, and impact of an attack, allowing for a timely and effective response.
Early detection of DDoS attacks significantly minimizes their impact. Organizations equipped with robust monitoring solutions report an average mitigation time of just 30 minutes, while those lacking adequate monitoring capabilities face an average mitigation time of 4 hours or more.
By prioritizing regular security audits, implementing continuous monitoring, and leveraging SIEM systems, you establish a robust security foundation for your hosting environment. These practical steps enable you to proactively identify vulnerabilities, swiftly detect DDoS attacks, and respond effectively to ensure the ongoing safety of your hosting infrastructure.
X. Real-Life DDoS Attacks on Hosting and Their Solutions
In the realm of cybersecurity, real-life examples provide valuable insights into the impact of DDoS attacks on hosting providers and the measures taken to safeguard their services. By examining notable cases, we can learn from the experiences of others and understand the effectiveness of different mitigation strategies. Let’s delve into some intriguing stories and discover the solutions implemented to counter these attacks.
A. Description of notable DDoS attacks on hosting providers and the impact on their services
- Case Study: GitHub (2018)
In 2018, the popular code hosting platform GitHub was hit by one of the largest DDoS attacks ever recorded. The attack, known as the Memcached amplification attack, peaked at a staggering 1.35 terabits per second (Tbps) of traffic. This massive influx of data overwhelmed GitHub’s servers, resulting in intermittent service disruptions and slowdowns for millions of users. The attack highlighted the vulnerability of high-profile platforms and the need for robust DDoS protection measures.
- Case Study: Dyn (2016)
In 2016, domain name system (DNS) provider Dyn became the target of a widespread DDoS attack that impacted numerous major websites and online services. The attack involved a botnet known as Mirai, which flooded Dyn’s servers with a massive volume of malicious traffic. As a result, popular websites like Twitter, Spotify, and Reddit experienced significant outages, disrupting user access for several hours. This attack underscored the potential cascading effects of targeting critical infrastructure.
B. Examination of the mitigation techniques and solutions implemented to counter these attacks
- GitHub’s Response
Following the DDoS attack, GitHub swiftly activated a combination of mitigation techniques to protect its infrastructure. They leveraged a multi-layered defense approach, including traffic filtering, rate limiting, and traffic rerouting. Additionally, GitHub collaborated with its upstream providers to absorb and mitigate the attack traffic. Their proactive response and collaboration with industry partners ensured minimal disruption and allowed them to quickly restore normal service operations.
- Dyn’s Response
In response to the Mirai botnet attack, Dyn employed various mitigation strategies to regain control and protect its DNS infrastructure. They implemented traffic filtering to block malicious traffic originating from the botnet. Additionally, Dyn collaborated with law enforcement agencies to track down the responsible individuals and disrupt the botnet’s operation. Their collaborative efforts mitigated the attack’s impact and prevented further disruptions.
C. Analysis of the effectiveness of the applied solutions and the resulting improvements in hosting security
The responses by GitHub and Dyn to these large-scale DDoS attacks demonstrate the effectiveness of comprehensive mitigation strategies. By combining traffic filtering, rate limiting, and collaboration with upstream providers, GitHub successfully mitigated the massive Memcached amplification attack. This incident highlighted the importance of proactive DDoS protection measures and the need for close cooperation within the industry to defend against evolving threats.
Similarly, Dyn’s response to the Mirai botnet attack showcased the significance of implementing traffic filtering techniques and collaborating with law enforcement agencies. Their actions not only mitigated the attack but also contributed to dismantling the botnet responsible for the disruption. This incident emphasized the importance of timely incident response and collaboration with external entities to neutralize DDoS threats effectively.
According to a report by Arbor Networks, DDoS attacks exceeding 100 gigabits per second (Gbps) increased by 140% in 2020, highlighting the growing severity of such attacks. This data emphasizes the need for robust mitigation strategies to protect hosting environments against the escalating threat landscape.
Furthermore, a study conducted by Akamai Technologies reveals that organizations that leverage cloud-based DDoS protection services experience an average reduction of 96% in attack traffic reaching their infrastructure. This statistic underscores the effectiveness of cloud-based mitigation solutions in shielding hosting environments from DDoS attacks.
By examining real-life DDoS attack scenarios and the corresponding solutions employed by hosting providers, we gain valuable insights into effective mitigation strategies. The success stories of GitHub and Dyn exemplify the importance of a multi-layered defense approach, proactive response, and collaborative efforts in mitigating the impact of DDoS attacks and safeguarding hosting environments.
XI. Emerging Threats and Advanced Solutions for Hosting Security
As the landscape of DDoS attacks continues to evolve, it’s crucial for hosting providers to stay ahead of the curve by understanding emerging threats and adopting advanced solutions to bolster their security defenses. In this section, we will explore the latest DDoS attack vectors and techniques targeting hosting environments, introduce advanced DDoS mitigation tools and services, and delve into the exciting realm of machine learning and AI-driven solutions for detecting and mitigating sophisticated DDoS attacks.
A. Evolving DDoS Attack Vectors and Techniques Targeting Hosting Environments
DDoS attackers are constantly devising new strategies to exploit vulnerabilities in hosting infrastructure. It’s essential to stay informed about these emerging threats to effectively safeguard your hosting environment. Here are some notable attack vectors and techniques to be aware of:
- IoT Botnets: The proliferation of insecure Internet of Things (IoT) devices has provided attackers with a powerful arsenal for launching large-scale DDoS attacks. Compromised IoT devices are frequently enlisted in botnets, which can be directed to flood hosting environments with malicious traffic.
- Application Layer Attacks: Unlike traditional volumetric attacks, application layer attacks target specific vulnerabilities in web applications, APIs, or underlying infrastructure. These attacks are often challenging to detect and can bypass traditional security measures.
- SSL/TLS Attacks: Attackers have started exploiting weaknesses in the SSL/TLS encryption protocols to launch DDoS attacks. By overwhelming server resources with resource-intensive SSL/TLS handshakes, they can disrupt hosting services.
B. Introduction to Advanced DDoS Mitigation Tools and Services for Enhanced Hosting Security
To combat the evolving DDoS threat landscape, advanced DDoS mitigation tools and services have emerged. These solutions offer enhanced capabilities to detect and mitigate sophisticated attacks, providing an additional layer of defense for hosting environments. Here are some notable tools and services:
- Behavioral Analysis: Advanced DDoS mitigation solutions leverage behavioral analysis techniques to detect anomalies in network traffic patterns. By establishing a baseline of normal behavior, these tools can identify and block malicious traffic in real time.
- Cloud-based DDoS Protection: Cloud-based DDoS protection services utilize the scalability and resilience of cloud infrastructure to absorb and filter out malicious traffic. By diverting traffic through their network, these services can mitigate the impact of attacks before they reach the hosting environment.
- Traffic Scrubbing Centers: Traffic scrubbing centers act as specialized filtering points, intercepting and analyzing incoming traffic to identify and mitigate DDoS attacks. These centers employ advanced algorithms and heuristics to differentiate legitimate traffic from malicious requests.
C. Exploration of Machine Learning and AI-Driven Solutions to Detect and Mitigate Sophisticated DDoS Attacks
Machine learning and AI-driven solutions have shown great promise in the battle against DDoS attacks. These technologies enable the automated detection and mitigation of complex and evolving attack patterns. By analyzing vast amounts of data and identifying anomalous behavior, machine learning algorithms can identify and respond to DDoS attacks in real time. This proactive approach minimizes response times and enhances the overall security posture of hosting environments.
According to a report by MarketsandMarkets, the global DDoS protection market is projected to reach $4.7 billion by 2025, with a compound annual growth rate (CAGR) of 16.5%. This growth is indicative of the rising demand for advanced DDoS mitigation solutions and underscores the need for hosting providers to embrace these technologies to ensure robust security.
By staying informed about emerging threats, adopting advanced DDoS mitigation tools and services, and exploring the potential of machine learning and AI-driven solutions, hosting providers can fortify their defenses against evolving DDoS attacks. These proactive measures help safeguard the availability and reliability of hosting services, providing peace of mind to businesses and users alike.
XII. Conclusion
As we conclude our discussion on securing your hosting against DDoS attacks, let’s recap the crucial points we’ve covered and highlight the significance of implementing robust security measures in hosting environments. DDoS attacks pose a serious threat to the availability and performance of your hosting services, making it imperative to stay proactive and vigilant in safeguarding your infrastructure.
Throughout this guide, we’ve explored the intricate relationship between hosting environments and DDoS attacks. Hosting providers, with their vast infrastructure and network resources, become prime targets for malicious actors seeking to disrupt online services. By overwhelming servers and network resources with massive amounts of traffic, DDoS attacks can render websites and applications inaccessible, causing significant financial and reputational damage.
The impact of DDoS attacks on hosting environments can be far-reaching, affecting businesses of all sizes and industries. Beyond the immediate disruption of services, these attacks can result in revenue losses, customer dissatisfaction, and damage to brand reputation. Therefore, taking proactive measures to protect your hosting environment is paramount.
By understanding the various types of DDoS attacks, their specific vulnerabilities, and the signs of an ongoing attack, you can better prepare your defenses. Implementing a multi-layered approach that combines DDoS mitigation techniques, network-level protections, and server security practices will significantly enhance your hosting security posture.
It’s essential to recognize that DDoS attacks are continually evolving, with attackers developing new strategies to exploit vulnerabilities in hosting infrastructure. As technology advances and the threat landscape evolves, hosting providers must stay informed and adapt their security measures accordingly.
Continuous monitoring, regular security audits, and staff education are vital components of a proactive security approach. By partnering with reliable hosting providers, implementing advanced DDoS mitigation tools, and exploring emerging technologies like machine learning and AI-driven solutions, you can stay one step ahead of potential attacks.
Remember, securing your hosting environment against DDoS attacks is an ongoing process that requires a combination of technical measures, staff awareness, and preparedness. By prioritizing security, you safeguard the availability, reliability, and reputation of your hosting services, ensuring a positive experience for your customers.
In conclusion, protecting your hosting against DDoS attacks is not an option but a necessity in today’s digital landscape. By implementing robust security measures, staying vigilant, and adapting to the ever-changing threat landscape, you can mitigate the risks associated with DDoS attacks and provide a secure hosting environment for your online presence. Stay proactive, informed, and prepared to defend your hosting infrastructure against the growing threat of DDoS attacks.


